In the realm of technology and national security, firmware codename classified programs represent a critical intersection of innovation and secrecy. Firmware, the specialized software embedded in hardware devices, plays a pivotal role in ensuring that systems operate efficiently and securely. However, when it comes to classified programs, the stakes are significantly higher.
These programs often involve advanced technologies that are integral to national defense and intelligence operations. The use of codenames for these firmware projects serves not only as a means of identification but also as a protective measure against unauthorized access and espionage. The classification of firmware programs is a necessary practice in an age where cyber threats are omnipresent.
By keeping the details of these programs under wraps, governments and organizations can safeguard sensitive information that, if exposed, could compromise national security. The codenames assigned to these firmware projects often carry a sense of intrigue and mystery, reflecting the complex nature of the technologies involved. As such, understanding the significance of these classified programs is essential for grasping the broader implications they have on security, technology, and international relations.
Key Takeaways
- Firmware codenames in classified programs are crucial for maintaining operational secrecy and national security.
- The history of classified firmware highlights its evolving role in advanced military and cybersecurity applications.
- Revealing firmware codenames poses significant ethical, legal, and security challenges.
- Classified firmware programs are integral to modern military operations and cybersecurity defenses.
- The future of these programs involves balancing transparency with the need to protect sensitive information.
The History of Classified Firmware Programs
The history of classified firmware programs can be traced back to the early days of computing when governments began to recognize the potential of technology in warfare and intelligence gathering. During the Cold War, for instance, the United States and its adversaries invested heavily in developing advanced computing systems that could process vast amounts of data and execute complex operations. As these systems evolved, so too did the need for secure firmware that could protect sensitive information from prying eyes.
Over the decades, the landscape of classified firmware programs has transformed dramatically. The advent of the internet and the proliferation of digital technologies have introduced new vulnerabilities, prompting governments to adopt more sophisticated methods for securing their firmware. This evolution has led to the establishment of various protocols and standards aimed at ensuring the integrity and confidentiality of classified programs.
As technology continues to advance at an unprecedented pace, the history of these programs serves as a testament to the ongoing battle between innovation and security.
The Role of Firmware in Classified Programs
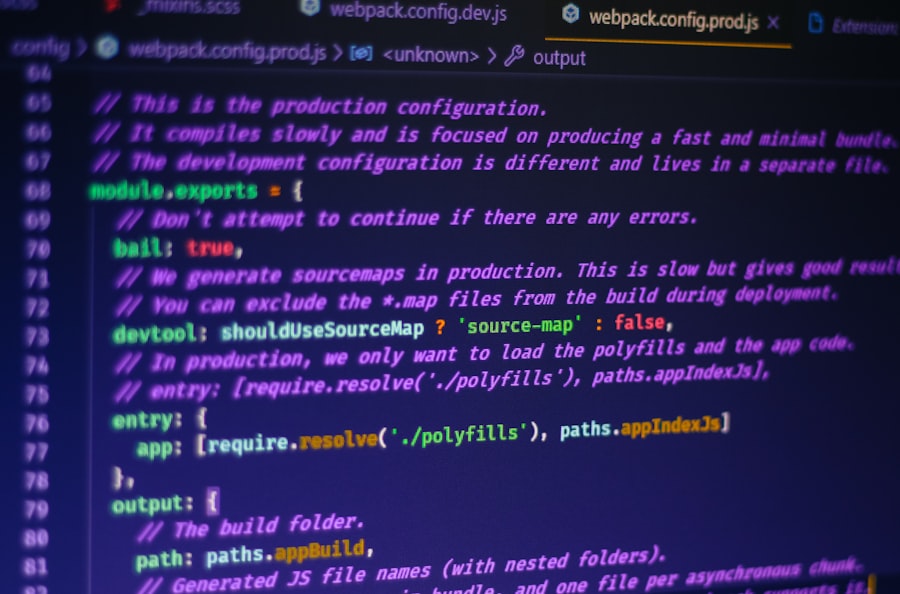
Firmware plays an indispensable role in classified programs by providing the foundational software that enables hardware devices to function effectively. In military applications, for example, firmware is responsible for controlling everything from weapon systems to communication devices. The reliability and security of this firmware are paramount, as any vulnerabilities could be exploited by adversaries, leading to catastrophic consequences.
Moreover, firmware is often designed with specific functionalities tailored to meet the unique requirements of classified operations. This customization allows for enhanced performance and security features that are not typically found in commercial off-the-shelf products. As a result, classified firmware programs often incorporate cutting-edge technologies such as encryption algorithms and secure boot processes to protect against unauthorized access and tampering.
The intricate relationship between firmware and hardware in these programs underscores the importance of maintaining stringent security measures throughout the development lifecycle.
The Importance of Keeping Firmware Codenames Classified
The practice of keeping firmware codenames classified is rooted in the need for operational security. By concealing the identities of these programs, governments can mitigate the risk of adversaries gaining insights into their capabilities and intentions. Codenames serve as a layer of abstraction that can obscure the true nature of a project, making it more challenging for potential threats to discern its purpose or functionality.
Additionally, classified codenames can help prevent leaks of sensitive information that could arise from discussions or documentation related to specific projects. In an era where information can be disseminated rapidly through digital channels, maintaining confidentiality is crucial for preserving strategic advantages. The use of codenames not only protects individual programs but also contributes to a broader culture of secrecy that is essential for national security operations.
The Challenges of Unveiling the Secrets of Classified Firmware Programs
| Firmware Codename | Program Name | Version | Release Date | Security Level | Supported Devices | Notes |
|---|---|---|---|---|---|---|
| ShadowWolf | StealthOS | 3.2.1 | 2023-11-15 | Top Secret | Classified Comm Devices | Enhanced encryption module |
| IronClad | FortressFW | 5.0.0 | 2024-02-10 | Secret | Military-grade routers | Anti-tamper features included |
| NightHawk | SilentGuard | 2.7.4 | 2023-08-22 | Confidential | Surveillance drones | Low power consumption |
| SilverFox | QuickBoot | 1.9.8 | 2024-01-05 | Secret | Embedded systems | Fast startup optimization |
| BlackMesa | CoreShield | 4.3.3 | 2023-12-30 | Top Secret | Secure servers | Advanced intrusion detection |
Despite the efforts to keep classified firmware programs under wraps, there are significant challenges associated with unveiling their secrets. One major obstacle is the complexity of modern technology itself. As systems become increasingly intricate, understanding their inner workings requires specialized knowledge and expertise that may not be readily available to outsiders.
This complexity can create a barrier to transparency, making it difficult for even well-informed individuals to grasp the full scope of a program’s capabilities. Moreover, the legal frameworks surrounding classified information add another layer of difficulty. Whistleblowers and journalists who seek to expose potential wrongdoing or inefficiencies within these programs often face significant legal repercussions.
The fear of prosecution can deter individuals from coming forward with information that could shed light on questionable practices or ethical concerns. As a result, the challenges associated with unveiling classified firmware secrets highlight the tension between national security interests and the public’s right to know.
The Impact of Classified Firmware Programs on National Security

Classified firmware programs have a profound impact on national security by providing governments with advanced tools for defense and intelligence operations. These programs enable military forces to maintain technological superiority over adversaries, ensuring that they are equipped with state-of-the-art capabilities in an increasingly competitive global landscape. The development and deployment of secure firmware are essential for protecting critical infrastructure and sensitive data from cyber threats.
Furthermore, classified firmware programs can play a crucial role in countering emerging threats such as cyber warfare and terrorism. By investing in advanced technologies that incorporate robust security measures, governments can better defend against attacks that seek to exploit vulnerabilities in their systems. The strategic importance of these programs cannot be overstated; they are integral to maintaining national sovereignty and safeguarding citizens from potential harm.
The Ethical and Legal Implications of Revealing Classified Firmware Codenames
The decision to reveal classified firmware codenames raises significant ethical and legal implications that must be carefully considered. On one hand, transparency is essential for holding governments accountable and ensuring that they operate within legal boundaries. Whistleblowers who expose misconduct or inefficiencies within classified programs may argue that their actions serve the public interest by shedding light on potential abuses of power.
On the other hand, revealing such information can jeopardize national security and put lives at risk. The delicate balance between transparency and security is a contentious issue that often leads to heated debates among policymakers, legal experts, and civil rights advocates. As technology continues to evolve, navigating these ethical dilemmas will require thoughtful consideration of both the potential benefits and risks associated with disclosing classified information.
The Future of Classified Firmware Programs
Looking ahead, the future of classified firmware programs is likely to be shaped by several key trends in technology and security. As artificial intelligence (AI) and machine learning continue to advance, there will be increasing opportunities to integrate these technologies into firmware development processes. This integration could lead to more adaptive and resilient systems capable of responding dynamically to emerging threats.
Additionally, as cyber threats become more sophisticated, governments will need to prioritize investment in secure firmware solutions that can withstand attacks from state-sponsored actors and criminal organizations alike. The ongoing evolution of cybersecurity practices will necessitate a proactive approach to developing classified firmware programs that not only meet current needs but also anticipate future challenges.
The Relationship Between Classified Firmware Programs and Cybersecurity
The relationship between classified firmware programs and cybersecurity is inherently intertwined, as both domains share a common goal: protecting sensitive information from unauthorized access and exploitation. Classified firmware serves as a critical line of defense against cyber threats by ensuring that hardware operates securely and reliably within sensitive environments. As cyberattacks become more prevalent and sophisticated, maintaining robust cybersecurity measures within classified firmware programs is essential.
This includes implementing best practices such as regular updates, vulnerability assessments, and incident response protocols. By prioritizing cybersecurity within these programs, governments can enhance their overall resilience against evolving threats while safeguarding national security interests.
The Role of Firmware Codenames in Military Operations
In military operations, firmware codenames play a vital role in maintaining operational security and ensuring effective communication among personnel. These codenames allow military officials to discuss sensitive projects without revealing specific details that could compromise missions or strategies. By using codenames, military personnel can navigate discussions about classified technologies while minimizing the risk of leaks or misunderstandings.
Furthermore, codenames can foster a sense of camaraderie among team members working on classified projects. They create an internal culture where personnel feel connected to their work while also recognizing the importance of discretion in their roles. This sense of purpose can enhance morale and motivation among those involved in developing critical technologies for national defense.
The Ongoing Debate Surrounding Classified Firmware Programs
The ongoing debate surrounding classified firmware programs reflects broader societal tensions between security and transparency. As technology continues to evolve at an unprecedented pace, questions about the ethical implications of secrecy will remain at the forefront of discussions about national security policy. While classified firmware programs are essential for protecting sensitive information and maintaining strategic advantages, they also raise important questions about accountability and oversight.
Ultimately, finding a balance between safeguarding national interests and upholding democratic values will require ongoing dialogue among stakeholders from various sectors—government officials, technologists, ethicists, and civil society advocates alike. As this debate unfolds, it will shape not only the future of classified firmware programs but also the broader landscape of technology governance in an increasingly interconnected world.
You can read more about it in their detailed analysis here: XFile Findings.
WATCH THIS 🛑 LEAKED: The Ring That Defied Physics (1954-2025 Classified Documents Exposed)
FAQs
What is firmware in the context of classified programs?
Firmware is a type of software that is embedded directly into hardware devices to control their functions. In classified programs, firmware often contains sensitive code that manages secure operations and protects classified information.
What does the term “codename” mean in classified firmware programs?
A codename is a secret or project name assigned to a classified firmware program to conceal its true purpose and maintain operational security. It helps prevent unauthorized disclosure of the program’s details.
Why are firmware programs classified?
Firmware programs are classified to protect national security, proprietary technology, or sensitive operational capabilities. Classification restricts access to authorized personnel only, preventing espionage or tampering.
How is classified firmware typically protected?
Classified firmware is protected through encryption, access controls, secure storage, and strict handling procedures. Additionally, it may be developed and maintained within secure facilities to prevent leaks.
Can classified firmware be updated or modified?
Yes, but updates or modifications to classified firmware are tightly controlled and require authorization. The update process often involves secure channels and verification to ensure integrity and prevent unauthorized changes.
Who has access to classified firmware codenamed programs?
Access is limited to individuals with appropriate security clearances and a need-to-know basis. This includes certain government personnel, contractors, and engineers involved in the program.
What risks are associated with classified firmware programs?
Risks include unauthorized access, reverse engineering, malware insertion, and hardware tampering. Such risks can compromise security, reveal sensitive information, or disrupt critical systems.
How are classified firmware codenames chosen?
Codenames are typically selected to be non-descriptive and unrelated to the program’s function. They may be random words, acronyms, or thematic names designed to obscure the program’s true nature.
Is it possible for the public to learn about classified firmware programs?
Details about classified firmware programs are generally not disclosed to the public. Information may only become available through official declassification, leaks, or authorized disclosures.
What industries commonly use classified firmware codenamed programs?
Classified firmware is commonly used in defense, aerospace, intelligence, telecommunications, and critical infrastructure sectors where security and confidentiality are paramount.