The Five Eyes alliance, a clandestine network of intelligence sharing among Australia, Canada, New Zealand, the United Kingdom, and the United States, has long operated in the shadows of global security. Recently, however, reports have emerged suggesting an expansion of its capabilities, particularly concerning the collection and sharing of biometric data. This article will delve into the implications of this burgeoning trend, examining the types of biometric data involved, the mechanisms of sharing, the stated justifications, and the potential consequences for civil liberties and privacy.
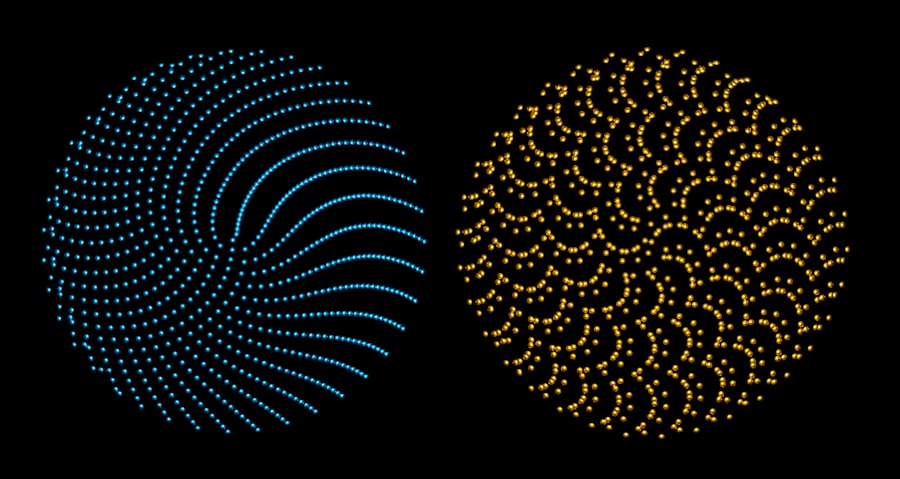
The term “biometrics” refers to the measurement and statistical analysis of unique physical and behavioral characteristics, such as fingerprints, facial recognition, iris scans, and voice patterns. These characteristics are, in theory, impossible to misplace or forget, offering a seemingly foolproof method of identification. Historically, the Five Eyes alliance has focused on signals intelligence, the interception and analysis of communications. However, the digital revolution has blurred the lines between physical and digital identities, paving the way for a more encompassing approach to intelligence gathering.
The Evolution from Signals Intelligence to Physical Identification
The initial mandate of the Five Eyes was rooted in the Cold War, primarily focused on monitoring and countering Soviet influence. Their strength lay in decrypting enemy communications and understanding their technological capabilities. As the global threat landscape has evolved, so too have the methodologies employed by these intelligence agencies. The rise of sophisticated surveillance technologies, often developed and deployed in the private sector and subsequently adopted by governments, has presented new avenues for intelligence acquisition.
From Cryptography to the Human Blueprint
While the early days of Five Eyes were about cracking codes and understanding coded messages, the contemporary focus is shifting towards understanding the coded messages inherent within human beings themselves. The digital footprint left by individuals – their online activities, communications, and even their physical movements captured by CCTV – is increasingly being augmented by the indelible markers of their biological selves. This represents a significant leap from deciphering human communication to directly reading human identity.
The Digital Trail and the Biological Marker
The digital trail, a persistent shadow cast by our online interactions, has long been a target for intelligence agencies. Every click, every search, every message creates a data point that, when aggregated, can paint a surprisingly detailed picture of an individual’s life, habits, and associations. The integration of biometric data with this existing digital trail creates a far more potent and comprehensive surveillance apparatus. It is akin to adding a unique, unforgeable fingerprint to an already extensive dossier.
Convergence of Digital and Physical Surveillance
This convergence is not accidental. Advances in artificial intelligence and machine learning have made it possible to process vast quantities of biometric data with unprecedented speed and accuracy. Facial recognition software, for instance, can now scan crowds and identify individuals against watchlists in real-time. Similarly, voice recognition can be used to authenticate individuals during phone calls or to transcribe and analyze conversations for keywords and sentiment.
The Scale of Data Collection: A Growing Reservoir
The sheer volume of biometric data being collected globally is staggering. From the mandatory fingerprinting for passport applications and visa processes to the ubiquitous presence of facial recognition cameras in public spaces, individuals are passively, and sometimes actively, contributing to this ever-expanding reservoir. The question then becomes what happens to this data once it is collected, and crucially, who has access to it.
The Data Deluge: From Personal to National Security
The data deluge is not merely a trickle; it is a veritable ocean. Every individual, through their daily interactions with technology and their presence in public spaces, is contributing to this growing reservoir. This data, when analyzed in conjunction with traditional intelligence, can offer insights that were previously unimaginable. The challenge for governments, and indeed for citizens, is to navigate the ethical and practical implications of such pervasive data collection.
Automation and AI: The Engine of Analysis
The sophisticated analytical capabilities afforded by automation and artificial intelligence are crucial to making sense of this immense dataset. Without these tools, the collected biometric data would remain largely inert. AI algorithms are the tireless miners of this digital and biological goldmine, extracting patterns, making connections, and flagging potential threats.
The topic of biometric data sharing among the Five Eyes alliance has garnered significant attention, particularly in light of privacy concerns and national security implications. For a deeper understanding of this issue, you can refer to a related article that explores the complexities and ramifications of such data sharing practices. To read more about it, visit this article.
Mechanisms of Biometric Data Sharing Within Five Eyes
The precise mechanisms by which biometric data is shared between Five Eyes nations remain largely opaque, a characteristic inherent to intelligence alliances. However, common intelligence sharing agreements and established protocols provide a framework for understanding how this could and likely does occur. The principle of “all-source intelligence” suggests a comprehensive approach, integrating various data streams.
The Fusion of Databases: A Comprehensive Dossier
Imagine intelligence agencies maintaining separate overflowing filing cabinets, each containing pieces of the same puzzle. The sharing of biometric data within Five Eyes can be understood as the process of consolidating these cabinets into one colossal, interconnected archive. This fusion allows for a more holistic understanding of individuals and their potential activities, bridging geographical and jurisdictional boundaries.
Bilateral and Multilateral Agreements
While not explicitly public, it is highly probable that the Five Eyes alliance operates under a complex web of bilateral and multilateral agreements that govern the exchange of intelligence, including biometric data. These agreements would outline what types of data can be shared, under what circumstances, and with what safeguards. The foundational agreement, the UKUSA Agreement (also known as the BRUSA Agreement), signed in 1946, laid the groundwork for extensive intelligence cooperation and continues to evolve.
Interoperability of Systems
A key aspect of effective data sharing is the interoperability of the systems used by each member nation. This means that databases maintained by agencies in one country must be able to communicate and integrate with databases in another. This can be technically challenging, requiring standardized data formats, protocols, and robust cybersecurity measures to prevent unauthorized access.
The recent discussions surrounding Five Eyes biometric data sharing have raised important questions about privacy and security among member nations. An insightful article that delves deeper into this topic can be found at XFile Findings, where the implications of such data exchanges are explored in detail. As countries collaborate more closely on intelligence matters, understanding the balance between national security and individual rights becomes increasingly crucial.
The Role of Joint Operations and Investigations
In the context of joint counter-terrorism operations or transnational crime investigations, the sharing of biometric data would be a natural and indeed essential component. When an individual is suspected of involvement in activities that span multiple Five Eyes countries, the ability to compare their biometric identifiers against databases in each nation becomes a powerful investigative tool.
Cross-Border Fingerprint and DNA Databases
The sharing of fingerprint databases, for instance, is already a well-established practice in international law enforcement. The expansion to other biometric modalities, such as facial recognition databases or even voiceprint libraries, would represent a logical extension of this existing framework. This allows investigators to track individuals across borders with unprecedented efficiency.
Facial Recognition Networks and Watchlists
The development of interconnected facial recognition networks is a particularly potent example. If a suspect’s face is captured on camera in one Five Eyes country, that image can be instantaneously compared against databases in the other four, potentially leading to identification and apprehension. These networks can act as digital bloodhounds, sniffing out individuals of interest across vast geographical areas.
De-identification and Re-identification Challenges
A crucial aspect underpinning the sharing of data, particularly personal data, is the concept of de-identification. This involves removing personally identifiable information from datasets before they are shared, theoretically protecting individual privacy. However, the effectiveness of de-identification techniques is often debated, especially in the context of rich datasets that can be re-identified through sophisticated analytical methods.
The Illusion of Anonymity
The promise of anonymized data sharing is akin to believing a ghost cannot recognize its own shadow. While direct identifiers might be removed, the unique constellation of data points within a biometric profile, when combined with other contextual information, can often lead to re-identification. This is a significant concern for privacy advocates.
The Re-identification Arms Race
The race between data anonymization techniques and re-identification algorithms is an ongoing one. As anonymization methods become more sophisticated, so too do the algorithms designed to circumvent them. This creates a constant push and pull, with the ultimate security of personal data hanging precariously in the balance.
Stated Justifications for Biometric Data Sharing

The primary justifications for the Five Eyes alliance’s engagement with biometric data sharing invariably revolve around national security, counter-terrorism, and the prevention of transnational crime. These are legitimate concerns that underpin the need for effective intelligence gathering and international cooperation. However, the methods employed to address these concerns warrant rigorous scrutiny.
Combating Evolving Terrorist Threats
The global nature of terrorism necessitates a coordinated international response. Proponents of expanded biometric data sharing argue that it is a vital tool in identifying and tracking individuals who pose a threat to national security, particularly those who operate across borders. This allows intelligence agencies to connect the dots between seemingly disparate individuals and potential plots.
Threat Intelligence and Predictive Analysis
Biometric data, when integrated with other intelligence streams, can contribute to more robust threat intelligence. By identifying patterns of association or modus operandi across a number of individuals, intelligence agencies aim to develop more accurate predictive analysis of future threats. This can enable pre-emptive action, potentially averting attacks.
Identifying Foreign Fighters and Extremist Networks
The identification of foreign fighters who travel to conflict zones and subsequently return to their home countries is a significant challenge. Biometric data, such as facial recognition matches at border crossings or travel records linked to known individuals, can be instrumental in tracking these individuals and disrupting extremist networks.
Preventing Transnational Organized Crime
The interconnectedness of global trade and communication has also facilitated the rise of transnational organized crime. Drug trafficking, human trafficking, and cybercrime often operate across multiple jurisdictions, making them difficult to combat without international cooperation. Biometric data can aid in identifying individuals involved in these criminal enterprises and disrupting their operations.
Tracking Criminal Networks Across Borders
Just as with terrorist threats, the ability to track the movement and identification of individuals involved in organized crime across borders is crucial. Biometric data can help to establish links between individuals and criminal organizations operating in different Five Eyes countries, leading to more effective disruptions and prosecutions.
Countering Identity Fraud and Forgery
Biometric identification offers a robust method for countering identity fraud and forgery, which are often used to facilitate criminal activities. By verifying an individual’s identity against immutable biological characteristics, law enforcement agencies can prevent criminals from operating under false pretenses.
Enhancing Border Security and Immigration Control
For nations with significant borders, the effective management of immigration and the prevention of illegal entry are paramount. Biometric data, such as fingerprints and facial scans collected upon entry or during visa applications, can be used to create secure passenger manifests, identify individuals with previous immigration violations, and prevent those deemed a security risk from entering the country.
Secure Identification at Ports of Entry
The implementation of biometric systems at airports, seaports, and land borders ensures that individuals are who they claim to be. This enhances the accuracy of traveler identification and reduces the risk of individuals entering countries under false pretenses.
Streamlining Legitimate Travel While Identifying Risks
While the focus is often on identifying risks, biometric systems, when efficiently implemented, can also streamline legitimate travel by enabling faster processing of travelers who are pre-vetted or do not present a security concern. This is a delicate balancing act between security and convenience.
Privacy Concerns and Civil Liberties Implications
The expansive collection and sharing of biometric data, while touted for its security benefits, raises significant concerns regarding individual privacy and civil liberties. The potential for misuse, mass surveillance, and the erosion of fundamental rights is a critical aspect that warrants careful consideration.
The Erosion of Privacy in a Surveillance Society
The widespread deployment of biometric surveillance technologies creates an environment where individuals can feel constantly observed. The ability to track movements, identify individuals in public spaces, and link these identifiers to their digital lives can lead to a chilling effect on freedom of expression and association. It is as if the walls have eyes, not just ears, and those eyes are watching everyone, all the time.
Mass Surveillance and the Normalization of Monitoring
The proliferation of facial recognition cameras in cities, coupled with the potential to link these feeds to biometric databases, creates the infrastructure for mass surveillance. This normalization of constant monitoring can fundamentally alter the relationship between the individual and the state, shifting the balance heavily towards the latter.
The Chilling Effect on Dissent and Free Speech
When individuals know they are being monitored, they may be less likely to engage in activities that could be perceived as critical of the government or authority. This “chilling effect” can stifle public discourse, limit protests, and ultimately undermine democratic processes. The fear of being flagged or scrutinized can be a powerful deterrent to free expression.
The Risk of Misidentification and False Positives
Biometric technologies, while increasingly accurate, are not infallible. Errors can occur, leading to misidentification, wrongful accusations, and potential harassment. The consequences of a false positive can be severe, ranging from inconvenience and embarrassment to wrongful arrest and detention.
The Fallibility of Algorithms
Algorithms are trained on data, and if that data contains biases or is incomplete, the algorithms themselves can become biased. This can lead to disproportionate misidentification of certain demographic groups. The human element in reviewing flagged individuals is crucial, but the sheer volume of data can sometimes strain this oversight.
Consequences for Individuals and Communities
For individuals who are misidentified, the consequences can be devastating, impacting their reputation, employment, and personal freedom. When these errors disproportionately affect certain communities, it can exacerbate existing societal inequalities and erode trust in law enforcement and government institutions.
Data Security and the Potential for Abuse
The centralization of vast amounts of sensitive biometric data creates an attractive target for malicious actors. The risk of data breaches, hacking, and insider abuse is ever-present. If this data falls into the wrong hands, the consequences for individuals could be catastrophic, leading to identity theft, blackmail, and other forms of exploitation.
The Vulnerability of Centralized Databases
Centralized databases, while efficient for sharing, also represent a single point of failure. A successful breach of such a repository could expose the biometric data of millions of individuals, making them vulnerable to a wide range of malicious activities.
The Challenge of “Insider Threat”
Beyond external threats, the possibility of misuse by individuals within the intelligence agencies themselves cannot be discounted. Strict access controls, robust oversight, and ethical guidelines are essential, but the potential for abuse remains a significant concern.
The Lack of Transparency and Accountability
A significant challenge in assessing the implications of Five Eyes biometric data sharing is the inherent secrecy surrounding intelligence operations. This lack of transparency makes it difficult for the public, and indeed for elected representatives, to understand the full scope of data collection, the specific technologies employed, and the mechanisms of accountability.
Limited Public Oversight
The classified nature of intelligence activities limits the extent to which the public can oversee the implementation and impact of biometric data sharing. This raises questions about whether democratic principles of accountability are being adequately upheld.
The Need for Robust Legal Frameworks
The rapid evolution of biometric technologies has often outpaced the development of legal and ethical frameworks to govern their use. Ensuring that robust legal safeguards are in place to protect individual rights and provide avenues for redress is crucial in the face of expanding surveillance capabilities.
The Five Eyes alliance’s foray into the world of biometric data sharing represents a significant evolution in the landscape of intelligence gathering. While proponents highlight its potential to enhance national security and counter evolving threats, the implications for privacy and civil liberties are profound and warrant continuous public discourse and rigorous governmental oversight. The delicate balance between security and liberty, particularly in the age of pervasive digital and biological surveillance, is a challenge that will continue to define the relationship between the state and its citizens for years to come.
FAQs
What is the Five Eyes alliance?
The Five Eyes is an intelligence alliance comprising five countries: the United States, the United Kingdom, Canada, Australia, and New Zealand. These countries collaborate on intelligence sharing and security matters.
What type of biometric data is shared among the Five Eyes countries?
The Five Eyes countries share various types of biometric data, including fingerprints, facial recognition data, iris scans, and DNA profiles, to enhance security and law enforcement cooperation.
Why do the Five Eyes countries share biometric data?
They share biometric data to improve counterterrorism efforts, prevent crime, enhance border security, and facilitate the identification of individuals across member countries.
Are there privacy concerns related to Five Eyes biometric data sharing?
Yes, there are concerns about privacy, data security, and potential misuse of biometric information. Critics worry about the lack of transparency and oversight in how data is collected, shared, and used.
How is biometric data protected within the Five Eyes framework?
Each member country has its own legal frameworks and data protection measures. Additionally, agreements within the Five Eyes alliance set protocols for secure data exchange, but the specifics vary and are often classified.
